SeriousSam
As if we didn’t have enough to worry about, Microsoft has announced they are working on fixing another vulnerability in their software. Known as SeriousSam or HiveNightmare, it is a high severity zero-day elevation of privilege vulnerability in Windows currently under investigation by Microsoft. It is considered a zero-day vulnerability that can let attackers gain administration rights on vulnerable systems and execute capricious code with system privileges, according to Sergiu Gatlan of Bleeping Computer.
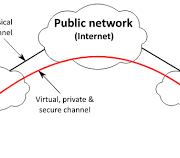
Zero-Day Vulnerability
In the world of cybersecurity, vulnerabilities are unintended flaws found in software programs or operating systems. A zero-day vulnerability is one that was just found by the software vendor, but no patch has been developed. Therefore, the threat is immediate and there are no days left to fix it. If left unaddressed, vulnerabilities create security holes that cybercriminals can exploit.
SeriousSam
SeriousSam, a Zero-Day security flaw, affects Windows 10 versions released since 2018. It also affects the not yet released Windows 11 version.
Using this vulnerability, hackers can access files that are stored under the C:\Windows\system32\config folder. Once accessed, the hackers can then obtain an account’s Windows New Technology Manager (NTLM) password and gain higher privileges via a pass-the-hash attack. With this attack, the plain text password is not necessary as is normally the case. Only the hash is required to gain access.
According to Wikipedia, SeriousSam replaces the need for stealing the plaintext password with merely stealing the hash and using that to authenticate entrance to the system. The hackers can then gain administrator rights on vulnerable systems – enabling them to install malware, applications, delete files, and much more.
Worse yet, hackers are already aware of how they can leverage the flaw. “That means Microsoft is in a race against the hackers – to fix the problem before too many people fall victim to hackers exploiting the issue.” (Aaron Brown, https://tinyurl.com/7kwk8ssv)
Microsoft’s Recommendations
While attackers can’t directly access the databases due to access violations triggered by the files always being in use by the OS, they can access them through shadow volume copies.
Microsoft recommends restricting access to the problematic folder AND deleting Volume Shadow Copy Service (VSS) shadow copies to mitigate this issue.
Here’s how to block the hackers until a fix is found:
Restrict access to the contents of %windir%system32config:
- Open Command Prompt or Windows PowerShell as an administrator.
- Run this command: icacls %windir%system32config*.* /inheritance:e
Delete Volume Shadow Copy Service (VSS) shadow copies:
- Delete any System Restore points and Shadow volumes that existed prior to restricting access to %windir%system32config
- Create a new System Restore point (if desired)
What to Look Out For
While the workaround will keep your machine safe, there are some side effects of which you should be aware. Deleting these shadow copies from your systems – as explained above – will impact some system and file restore operations. For example, if you use a third-party backup app to restore data or if you or your business relies on a third-party backup solution, it might be worth swerving the workaround for the time being.
Ways to Protect Your Data in the Future
According to Norton, following this security checklist below will make sure you are doing everything you can to help keep your information protected from the security risks associated with zero-day vulnerabilities in the future:
- Keep software and security patches up to date by downloading the latest software releases and updates. Installing security patches fixes bugs that the previous version may have missed.
- Establish safe and effective personal online security habits.
- Configure security settings for your operating system, internet browser, and security software.
- Install proactive and comprehensive security software to help block known and unknown threats to vulnerabilities.
Need Help?
If you are not sure what to do, or simply don’t want to be bothered, give us a call. WorkforceITJax is ready to help you with this and other issues.