Posts

With 2FA You Thought You Were Safe
2FA, Hacks, Phishing, Privacy, Security, UncategorizedBack in August 2020, we told you all about 2 Factor Authentication (2FA) and how it improves internet security. With 2FA you thought you were safe.
New Developments
You know the old saying “If you build it, they will come?” It can now…

3 WEEKS = 45 HACKS
Hacks, IT Insights, Privacy, Security, Uncategorized, WindowsDo you wonder which program is so insecure that it has been hacked 45 times in the last 3 weeks? Think Chrome.
Google recently announced that 20 new vulnerabilities have been found which brings the total to 45 in the last three weeks. Fifteen…

Can You Hear Me Now?
IT Insights, Mobile Devices, Privacy, SecurityRemember when Verizon used the phrase “Can you hear me now?” They were, of course, referring to their expanding network, but in today’s world, it appears to be more relevant to them hearing you. Why? Verizon enrolled customers into their…
PASSWORD MANAGERS TIME HAS COME
Hacks, IT Insights, Passwords, Security, Uncategorized, WindowsWe have all been lectured regarding the risks of using the same password over and over for our data. Corporate data, personal data. With the number of recent data hacks, there is a huge chance your passwords are on the dark web and available…

If You Didn’t Make This Purchase, Please Call Us
Email, Hacks, Mobile Devices, Security, Uncategorized, WindowsDo you shop online? If so, take notice. Scammers are sending emails that look amazingly like the real thing. One of the clues you want to look for to identify the email as spam is a phrase similar to this: “If you didn’t make this purchase,…

SeriousSam
Cyber Insurance, Hacks, IT Insights, SecurityAs if we didn’t have enough to worry about, Microsoft has announced they are working on fixing another vulnerability in their software. Known as SeriousSam or HiveNightmare, it is a high severity zero-day elevation of privilege vulnerability…
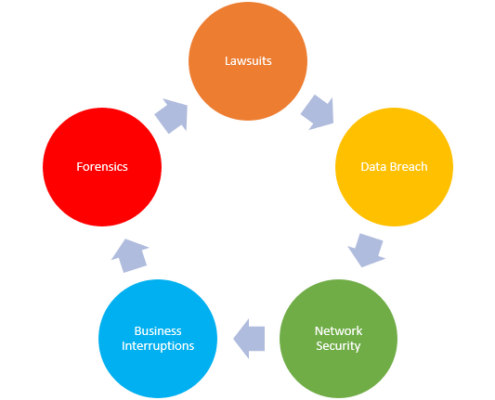
Cyber Insurance
Cyber Insurance, IT Insights, Phishing, SecurityYou have secured your data through a Virtual Private Network (VPN), security software, and strong passwords. Your personal and company information is safe, right? In other words, there is no need for Cyber Insurance.
Introduction
Really? In…

Mobile Device Security
Email, Mobile Devices, Phishing, SecurityMany of our posts have been about IT security, focusing on PCs and laptops. However, with the rapidly changing technology and portability of mobile devices, it is time to focus on mobile device security.
With recent global health events resulting…
Email Security Best Practices
Email, IT Insights, Pharming, Phishing, SecurityWhether your business is large or small, the number of emails you send and receive daily is probably quite large. In fact, on average,121 business emails are sent or received by employees every day. Have you taken steps to ensure your email…


